How Do Hackers Hack?
- HackingHackers

In 1993, sat in a friend’s bedroom as a spotty teen, I downloaded a file – how to hack.
This was the first time I had read anything about hackers. It intrigued me. I understood there were ways to program computers to make the computer games that I loved playing, and do typing for offices… But hacking. Breaking into a computer. That was new. What was it all about?
The file was short and didn’t go into technical details – not that I would have understood. It explained there were 3 steps needed to hack a company.
- Find out as much information as possible. About the company, about the computer system… any details are useful.
- Find a weakness. Look at how the computer and the company works. What is broken? What doesn’t quite work as planned? Where is the company vulnerable?
- Exploit the vulnerability and get in.
I had a new superpower, a new way of looking at things. In the early 90s, homes didn’t have internet connections, and this information wasn’t widely known. At the time, I had the morals of a 13-year-old boy, so what could I do with this newfound knowledge?
Sat in the computer lab at school it was clear. How could I get into everyone else’s account? They had passwords… but how could I get their passwords? Could I guess them?
Luckily a teacher intervened before I started a life of cybercrime. It was great to learn how computer security worked, but here were the ground rules. We made a deal. I couldn’t hack into other student’s accounts. I could write a programme to guess passwords, but not find out what the ‘correct’ answers were.
I spent months slowly working through a well-thumbed book on how to write programmes in BASIC. Many lunch breaks were spent working out how to write a simple password guesser. Then the day came… using a list of words and names I had gathered together, my teacher ran the final test.
My naïve little programme correctly guessed 3 in every 10 passwords on the school network. Hacking a computer wasn’t that hard.
27 years later… nothing has changed
What is most surprising, looking back 27 years later is nothing has changed. Searching for how to hack will get you the same basic information. The words have changed a little (https://en.wikipedia.org/wiki/Kill_chain#The_cyber_kill_chain) as cyber security has become militarised, but the outline is the same.
Following the 3 steps, hackers can break-in.
How can Fresh Security help?
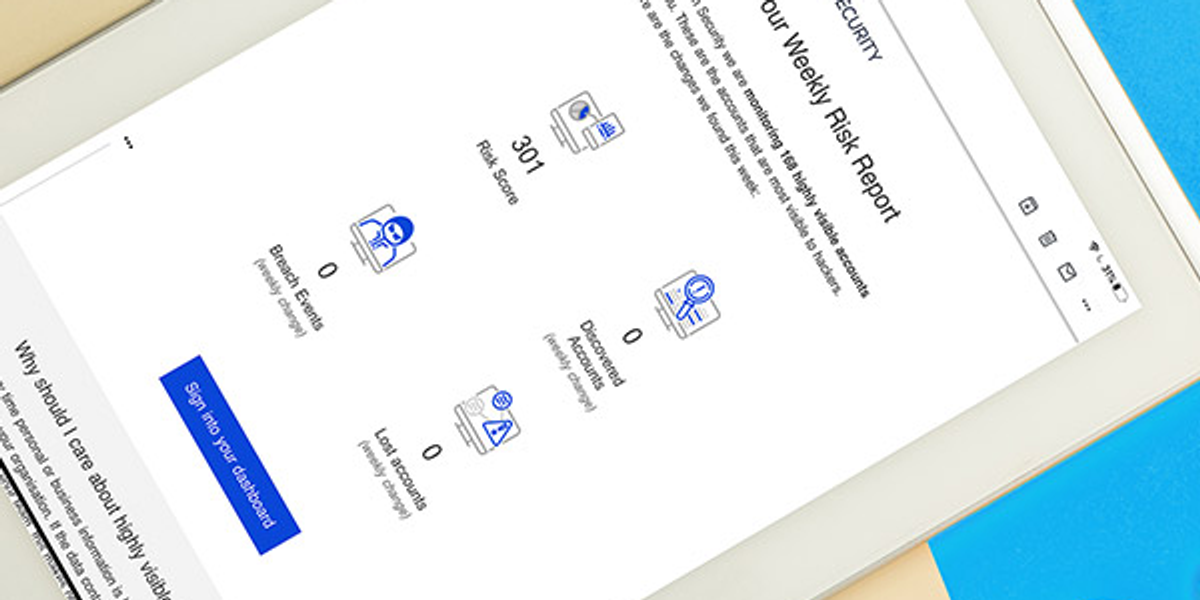
Fresh Security provides a hacker’s view of your organisation.
If you can answer - What can you find out about my company?
- Competitors find it harder to gather competitive intelligence against you.
- Your brand is more potent because the rough edges aren’t showing.
- Your security is improved by knowing what information a hacker can gather.
If you know - Which weaknesses need fixing?
- Stolen passwords can be changed before a hacker tries to use them to break-in.
- Computers can be configured so passwords can’t be reused, and as you use new services, the problem doesn’t return.
If you can tell - Who are the highly visible people?
- They can be warned that they are most likely to be the target of hackers. It means they can stay alert, and get more targeted cyber security training without increasing budgets.
Fresh Security helps you answer all three questions.