Fresh Thoughts #35: Who Represents Your Business?
- Newsletter
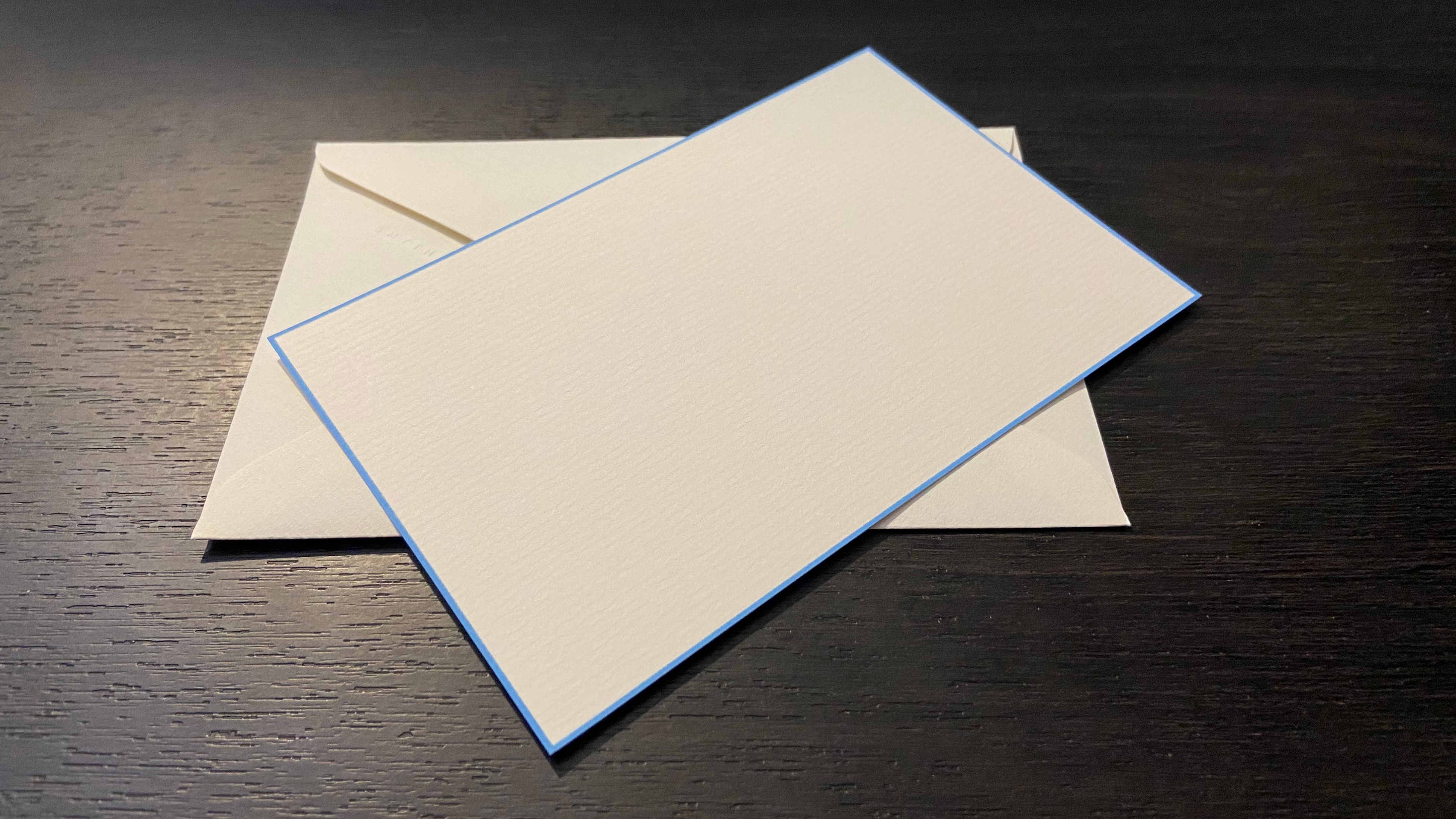
Every new Fresh Security customer receives a handwritten Thank You note.
Each note is unique, written in black ink on handmade paper with a thin Nile Blue border. The envelope is lined with Nile Blue tissue paper, handcrafted in England. It's a small token saying - we appreciate your trust, and this is the start of a personalised experience.
I always write the note. This is not something to delegate.
Writing one of these notes recently, I thought about who businesses allow to represent them...
Representative
When working with banks and governments, there is no delegation. The directors of the company represent the business.
Similarly, in schools - official letters to parents are signed by the head teacher. I notice the penned signature, even when they're scanned and sent via email. Am I the only one?
For less important letters - a Chief of Staff or another senior staff member may sign with a p.p.
It seems odd that paper letters - albeit scanned versions - still play a significant role in conducting business. However, we can't dodge the mainstay of modern business… the email.
Just like its physical paper predecessor, an email uses the idea of an envelope and letter in the underlying protocols. The envelope is often hidden from the reader. But remains - if you know where and what you're looking at.
The list starts to get long when we look at who can represent you and send emails on your behalf.
It's rare to find an email server hosted by a company these days. (Aside: If you're hosting your own Exchange Server, please ensure you know about the current Microsoft Exchange vulnerabilities 😬). So the task of sending daily emails is likely delegated to Microsoft or Google.
Add marketing newsletters to your community, customers, or prospects, and any of a dozen other companies could be emailing on your behalf.
And, of course, there's the people management systems, billing systems, customer service systems, booking systems, security testing systems…
Maybe the question should be - Who can't send emails on our behalf?
This is the hole that phishers and scammers exploit.
Luckily there are solutions - if you choose to configure them.
You can control who can send email 'envelopes' on your behalf.
There's a standard called SPF (Sender Policy Framework), which allows you to publish your trusted email service providers to the world. It's a one-line policy posted to the world using DNS - the same way you tell the world how to access your website.
Similarly, you can control who can sign off the letter part of the email. This is usually a much smaller list of people and uses a protocol called DKIM (DomainKeys Identified Mail). Again, your intentions are published to the world using DNS.
So every company has SPF and DKIM configured - right?
Well... no.
In late 2020, we worked with an Irish partner looking to sell into the Irish health service. We found hse.ie didn't have an SPF record… and as they say, the rest is history.
If you'd like to read the detailed report on how a phishing email led to a ransomware attack that locked 80% of the Irish health services IT infrastructure, it's here: https://www.hse.ie/eng/services/news/media/pressrel/hse-publishes-independent-report-on-conti-cyber-attack.html.
Cybersecurity protocols like SPF and DKIM may appear to be "just one more bit of extra complexity". But they are a valuable tool to enforce who is permitted to represent your company on an internet scale.
Our customers have seen significant drops in phishing emails reaching their teams after setting these policies. The security return is well worth the effort of configuration.
If your team needs any help with the configuration, just reply to this email, and the Fresh Security team will be ready to help.


