What Is a Password Manager?
With many different accounts and logins, it can be challenging to remember all of your different passwords. A common solution is that people often pick really simple, easy-to-remember passwords. However, simple passwords make it easy for hackers and cybercriminals to steal your information and access your online accounts.
A password manager is a simple solution to this problem. A password manager is a virtual tool that helps people choose and store strong passwords. By storing strong passwords, you don't need to remember a confusing set of numbers and letters to log in. With a password manager, your team can ensure their accounts will be secure and easy to manage.
Why is a Password Manager Useful?
Password managers are useful for businesses since it makes it easy for staff to use more unique passwords. This helps to increase your company's cybersecurity and protect valuable data. The number of passwords the team will need to remember will also be reduced since the password manager will keep track of all the different passwords. This will help save your staff time when it comes to logging into websites. It will also relieve your staff from the burden of creating and remembering high-security passwords. That way, they don't have additional stress about cybersecurity.
The Problem with Passwords
As people have become more familiar with cybersecurity, passwords have become 'more difficult to remember, but easier for computers to break.' This was best put by the iconic xkcd webcomic.
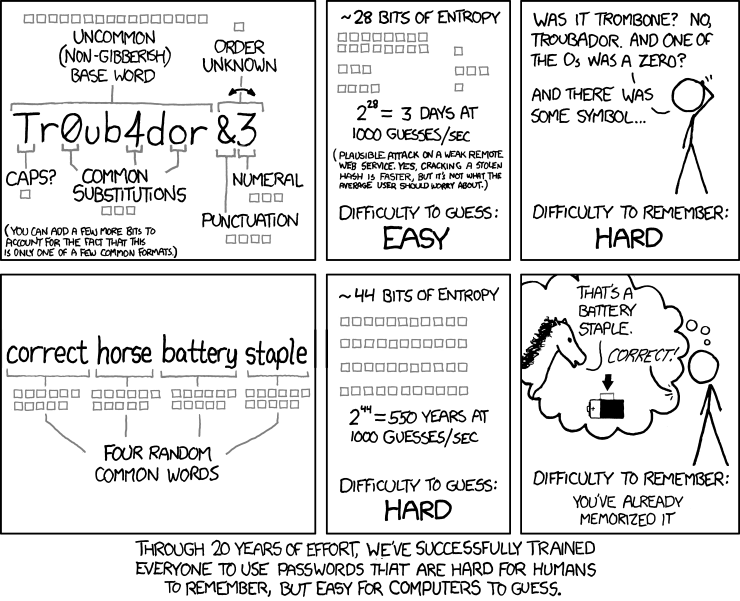
This comic shows that it is easy to guess words with common substitutes for the letters. It uses the example of Tr0ub4dor&3 as a substitute for Troubador. Passwords such as these are commonly used. Even though the symbols and letter replacements are difficult for people to remember, hackers can easily guess these passwords.
Passwords are not as secure when people choose them since people are predictable. People are likely to use easy to guess passwords such as 'password', '123456' or the names of their pets, parents, or the street they grew up on. With a password manager, the strong passwords will be truly random. That way, hackers can’t predict the password. It is important to note that these unique passwords are also easy to use. They will be recommended as a plug-in for each website, service, or app so that you don't need to remember the complex passwords.
Where can I get one from?
There are plenty of password managers to choose from. One way to get a password manager is to use a password manager application, such as 1Password, Lastpass, and Dashlane. The other option is to use a password manager with a browser or operating system. The passwords will automatically save with a browser extension.
Conclusion
Passwords are still necessary for many websites and computer systems, but they can be compromised. Simple and reused passwords make it easy for hackers to get valuable information from your company. That is why it is crucial to use 2-factor authentication wherever it is offered, especially for your sensitive accounts like banking, payments, and email. With a password manager, businesses can create and easily use strong passwords that are random and difficult to guess.


