Fresh Thoughts #85: In Pursuit of Novel and New
- Newsletter

New is exciting.
Imagine the possibilities...
In Pursuit of Novel and New
My son is becoming an inventor.
A long-time Lego fan - he is creating ever grander, novel and new ideas.
This weekend, we stopped for coffee.
Entering the cafe, he was chipper.
Suddenly - as we waited to be served - his mood switched to sulky and glum.
"What's wrong?"
After the fifteenth time of asking (he is developing selective deafness) he pointed out the window.
I saw it...
A van with a tent on top.

Three weeks ago - he had come home from school full of enthusiasm and excitement for his latest idea.
A tent...
on a car...
so you could move the tent wherever you wanted to go.
His idea would change how he could go on expeditions to discover new species of animals when he was older.
It was as revolutionary as any of his Lego creations.
Except it wasn't...
Because it wasn't a new, original idea.
He felt like the end of the world was nigh.
"Ok. I get it...
Look at it this way - you've saved 3 years of product development and testing.
Now - the critical question - what can you do with it?
It's not about the product. It's what you can do with it.
What could you achieve with it that you couldn't before?"
It made me think about cyber threat hunting...
Cyber Threat Hunting
As cybersecurity follows IT into being a commoditised "cost of doing business", the conversation has shifted.
Competition between security vendors is no longer about features or performance as a benchmark.
Cybersecurity marketing now asks us to spend time looking for threats in our systems.
Searching for spectres of potential problems.
To be clear - proactively searching for threats is a valuable task if you're in a high-risk industry.
Online banking, payment platforms, and government are continuously targeted by novel and new threats.
But for most businesses, I'm unconvinced that maintaining a covert presence in an elite Russian hacking forum is a key business objective.
I understand the challenge cybersecurity vendors face.
There is limited scope for new products.
Looking at the most frequent attack types reported in Verizon's Data Breach Investigation Report - 2023 - they have existing mitigations:
- Denial of Service: Protection service from telecom providers or companies like Cloudflare...
- Ransomware: EDR, timely patching, backups, segregation of networks...
- Use of stolen credentials: Dark-web monitoring, multi-factor or passwordless authentication...
- Phishing & Social engineering: Security awareness training & simulation...
- Exploit vulnerability: Vulnerability scanning, patching, penetration testing...
- Web application compromise: Secure development lifecycle, patching...
- Legacy multi-factor authentication bypass: device-based authentication...
As security product features become universal and cash cow products get bundled into services at "no extra costs" - what options are available?
The answer seems - to promote the idea that everyone is in a high-risk environment where only the novel and new matters or exists.
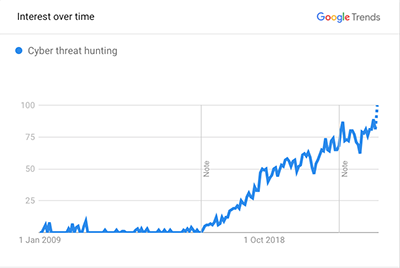
Today's novel and new is cyber threat hunting.
But as a business leader - I wonder...
When it comes to threat hunting in your systems - What does it achieve that you couldn't before?
And at what cost?


